Coordinated Subdomain Takeover Identified on NIMC Web Infrastructure
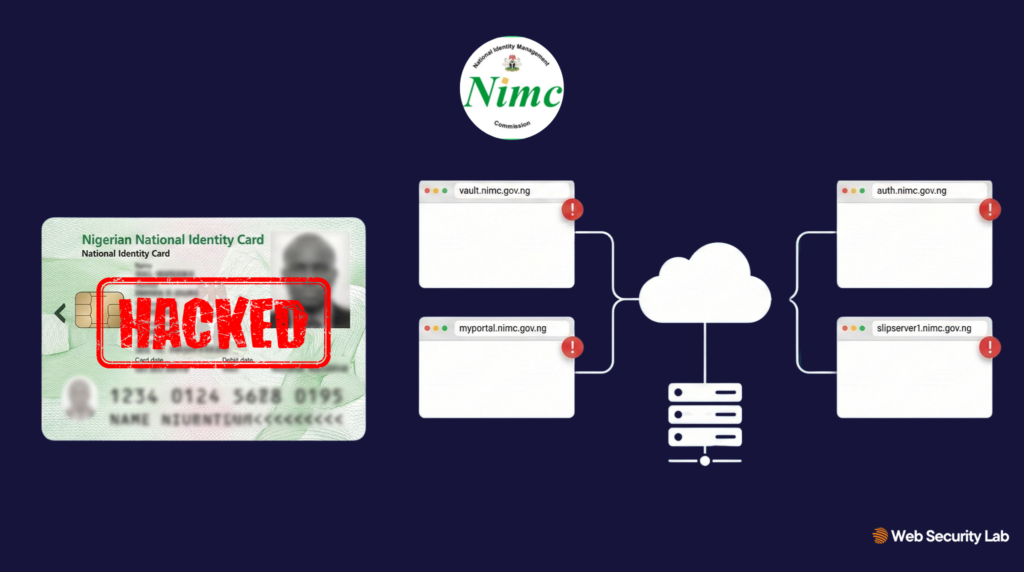
In the past few weeks, Web Security Lab has identified a pattern of suspicious activity affecting multiple subdomains operating under the National Identity Management Commission (NIMC) domain namespace.
What initially appeared to be an isolated anomaly has since developed into a broader case of coordinated subdomain abuse, involving spam, phishing, traffic monetisation redirects, and loss of administrative control across several web assets.
In both cases, affected subdomains resolved to IP ranges within DigitalOcean’s cloud infrastructure.
While cloud hosting providers are neutral service platforms, the recurrence of infrastructure clustering within the same provider ecosystem is a notable pattern indicator.
The NIMC was formally notified, and as of publication, it appears that remediation plans are well underway.
Discovery
The investigation began after anomalous search indexing was observed across the following NIMC subdomains:
vault.nimc.gov.ngdashboard.nimc.gov.ngmyportal.nimc.gov.ngauth.nimc.gov.ngpk.nimc.gov.ngslipserver1.nimc.gov.ngninslip.nimc.gov.ng
Unrelated content began appearing under trusted government URLs, including:
- Technology and entertainment articles
- Streaming login walkthroughs
- Adult-themed pages
- Software bypass tutorials
- Betting platform guides, etc.
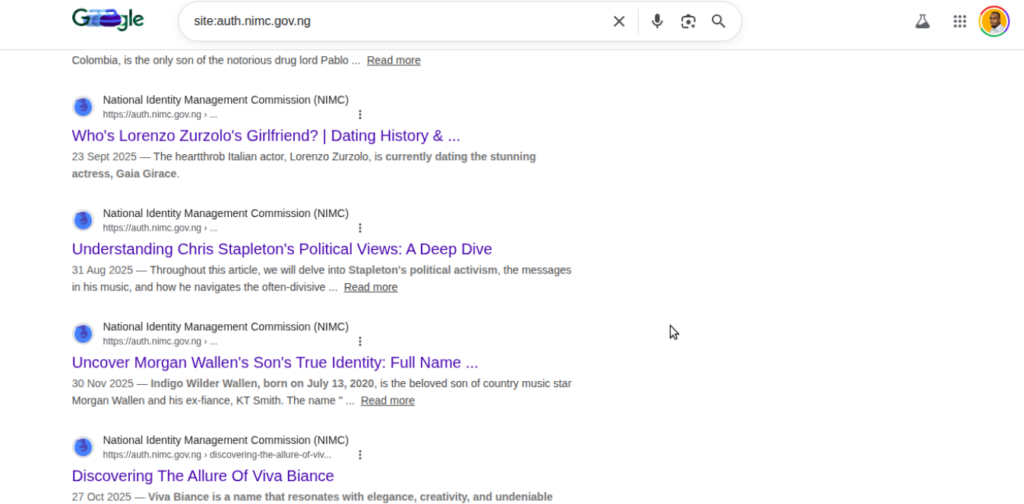
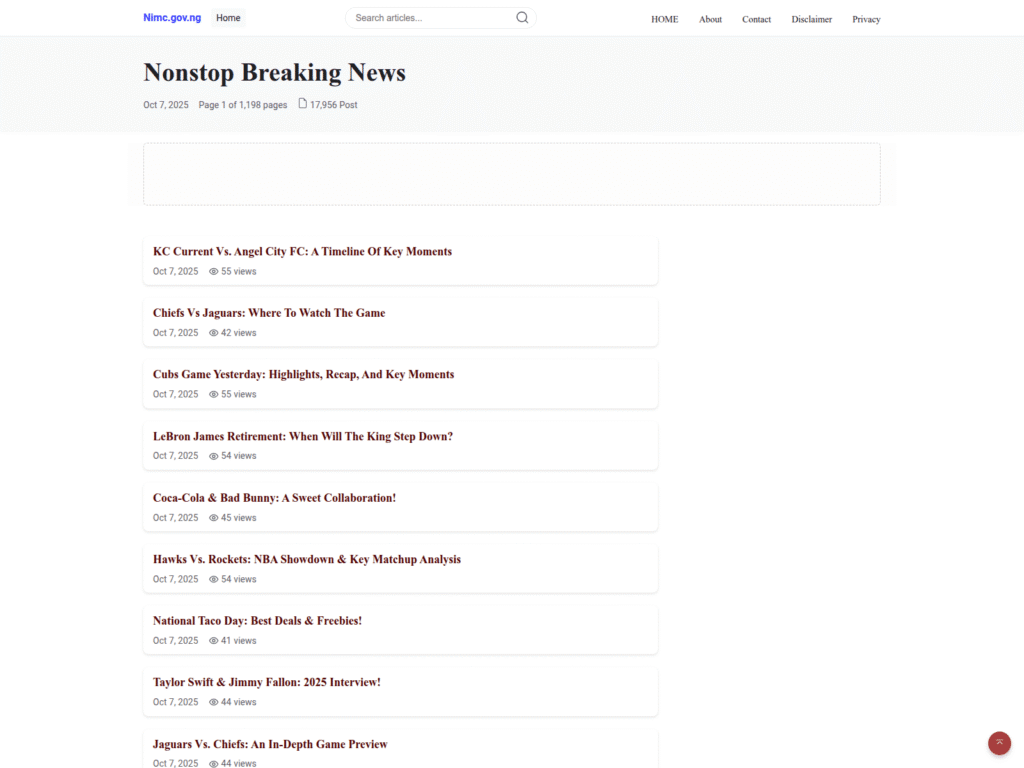
This content had no operational relationship to NIMC services, as snapshots and social media reports suggest that administrative control over the affected subdomains may have been lost by at least mid 2025.
This country is too useless dawg, why is the nimc app download website leading to this? pic.twitter.com/YNhwyj0cuu
— Adé’ Ògúnyalé | Real Estate Guy (@adeogunyale) April 29, 2025
SEO Infrastructure and Traffic Monetisation
One of the most heavily abused subdomains, vault.nimc.gov.ng, accumulated substantial search engine presence before remediation actions began.
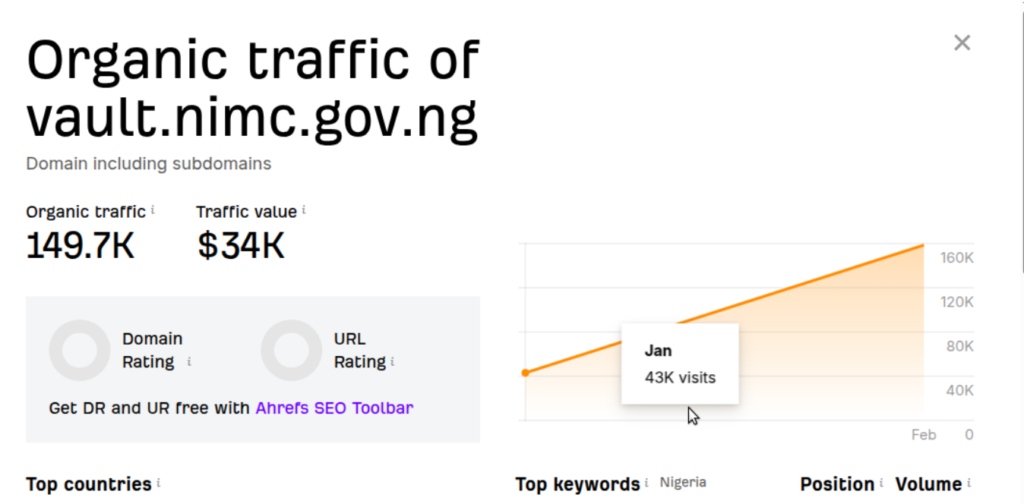
SEO intelligence data indicated:
- Over 149,000 organic search visits
- Hundreds of indexed pages
- Content spanning account creation guides, betting platforms, app tutorials, and device bypass tools
Several subdomains also transitioned from visible spam hosting to redirect-based traffic laundering.
LMFAOO Jesus this is page is a phishing page, it shows a fake "unable to connect" page and when you reload it, it points to a fishy download. Nigeria abeg https://t.co/ReQtrGwuqD
— ¿kofo? (@kofookesola) February 26, 2026
Observed redirect flow:
nimc subdomain
→ allfile.me
→ dicyclistclokemyoneure[.]com
Such redirect chains are commonly used to monetise residual search traffic, distribute malware, and to obscure infrastructure attribution
The presence of coordinated redirect behaviour reinforced the conclusion that the abuse was deliberate and organised.
Infrastructure Analysis
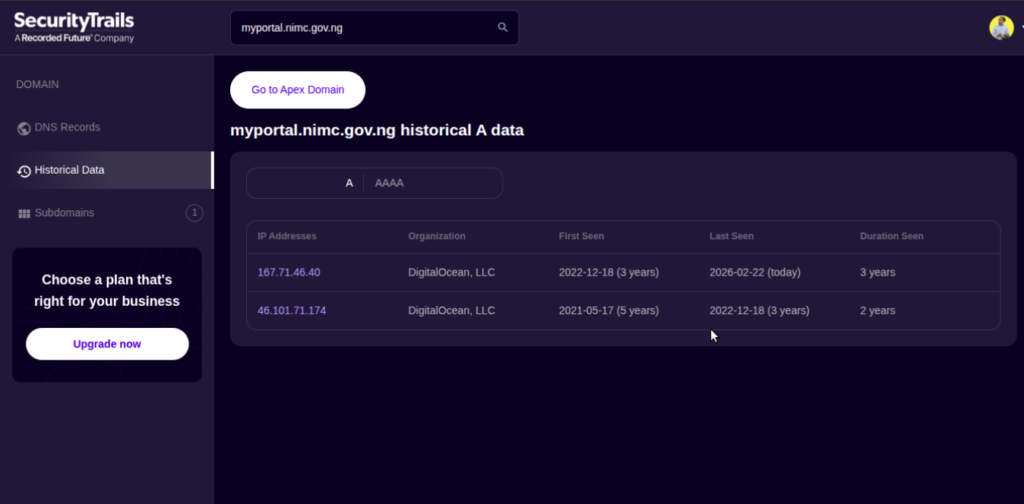
DNS resolution analysis revealed that multiple affected subdomains converged on closely-clustered cloud hosting infrastructure.
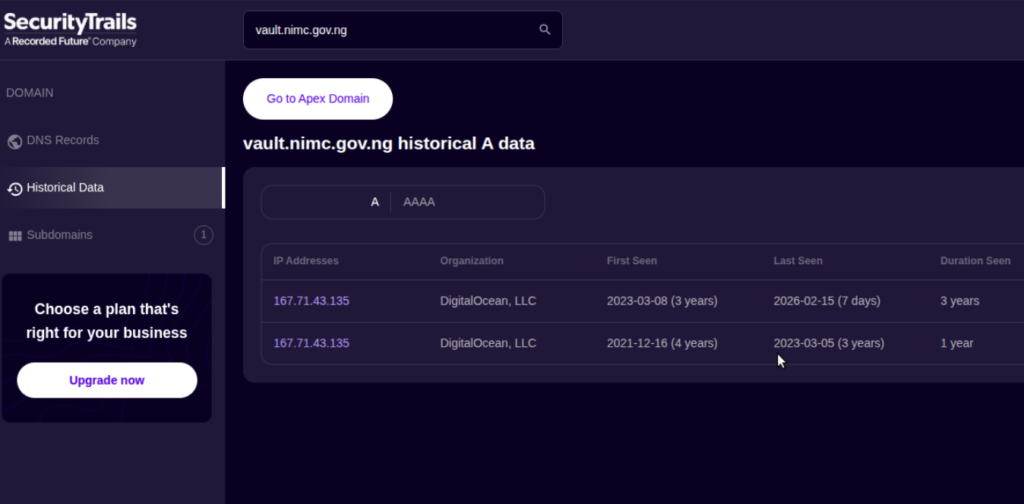
Observed IP associations include
- 167.71.46.40
- 167.71.43.135
- 167.71.39.215
The precise mechanism through which control of the affected subdomains was exercised cannot be determined through external analysis alone. Based on observable artefacts, potential pathways include infrastructure reuse, hosting account exposure, or misconfigured access controls.
Definitive attribution would require internal DNS logs, account-level audit trails, hosting control panel records, and administrative access history not available to this investigation.
It is equally important to state that this investigation found no evidence of intrusion into core NIMC systems or confirmed access to internal databases. Determining whether any internal systems were accessed would require direct forensic review by NIMC.
Broader Context and Trust Implication
This incident does not occur in isolation.
NIMC has previously faced sustained public criticism regarding the security and handling of Nigerians’ identity data, particularly in relation to National Identification Numbers (NIN) and Bank Verification Numbers (BVN).
Despite official denials of systemic compromise, identity data linked to Nigerians continues to circulate within underground marketplaces at extremely low prices. Web Security Lab can confirm that such marketplace activity remains active.
While the subdomain takeover described in this report is technically distinct from database compromise or identity record exposure, it contributes to ongoing public trust concerns surrounding Nigeria’s digital identity infrastructure.
Government domains carry strong reputational signals and search authority, making them attractive targets for SEO abuse, phishing infrastructure, and traffic monetisation operations. The misuse observed here aligns with a broader pattern of government web assets being targeted for exploitation of implicit public trust.
In environments where ownership of web assets is fragmented or lifecycle governance is unclear, exposure windows can persist for extended periods before detection.
The issue, therefore, is not simply technical. It is also structural.
Without enforced subdomain ownership, continuous monitoring, infrastructure inventory control, and clearly defined decommissioning processes, similar abuse is likely to recur.